What Data Privacy Laws Are In Your Country?
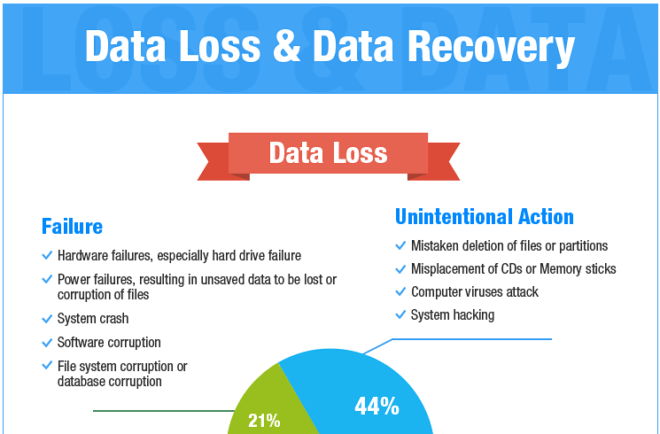
 Post thumbnail
Post thumbnail
Data Privacy is and continues to be a hot topic today. With the recent news of Amazon and Ring employees reviewing Echo and Ring user information, many consumers are concerned about what happens to their data. Who gives companies the right to review customer information and share it without their permission? Luckily, data privacy and…
Read More What Data Privacy Laws Are In Your Country?